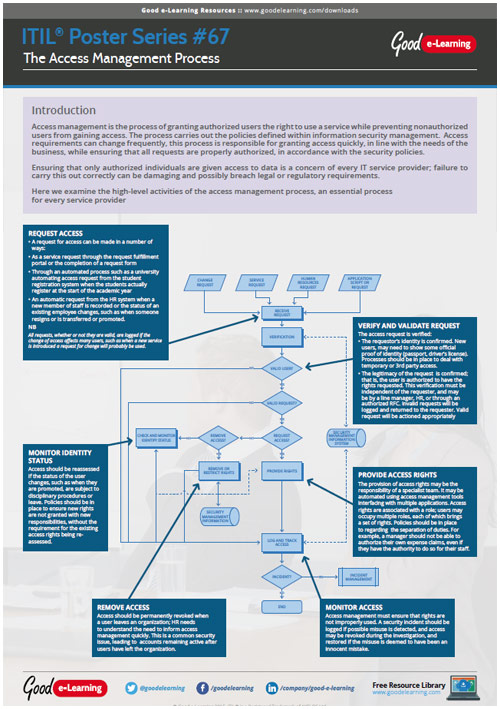

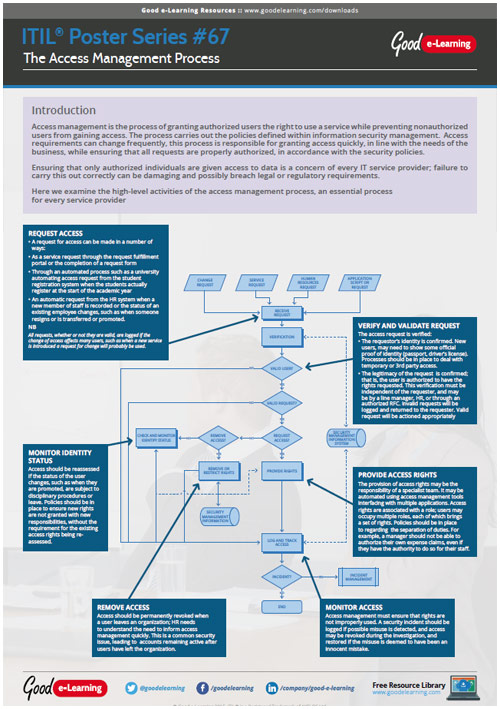
Access management is the process of granting authorized users the right to use a service while preventing nonauthorized users from gaining access. The process carries out the policies defined within information security management. Access requirements can change frequently, this process is responsible for granting access quickly, in line with the needs of the business, while ensuring that all requests are properly authorized, in accordance with the security policies.
Ensuring that only authorized individuals are given access to data is a concern of every IT service provider; failure to carry this out correctly can be damaging and possibly breach legal or regulatory requirements.
Here we examine the high-level activities of the access management process, an essential process for every service provider.
If this ITIL resource interests you, why not view our range of ITIL courses? Or view our full library of downloads covering a wide range of subjects and domains!
